MikroTik router to CISCO PIX Firewall IPSEC
Contents1 How to interconnect two networks with IPSec between Mikrotik ROS and Cisco PIX |
How to interconnect two networks with IPSec between Mikrotik ROS and Cisco PIX
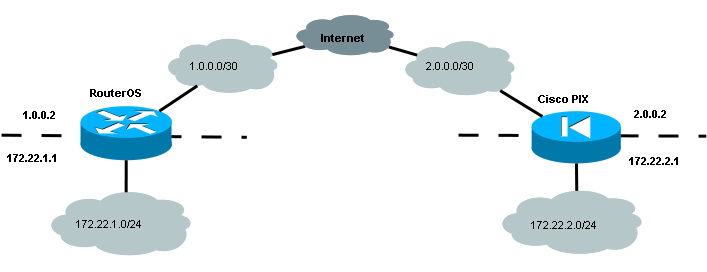
This example shows how to interconnect remote offices uses IPSec VPN between Mikrotik RouterOS device and Cisco PIX Firewall or Cisco Router, running Cisco IOS. Also I show you how to provide Internet access for network using masquerade/PAT on Mikrotik RouterOS, Cisco PIX Firewall and Cisco Router, running Cisco IOS. Network topology is shown below. We would like to interconnect networks 172.22.1.1/24 and 172.22.2.1/24 using corresponding public addresses 1.0.0.2 and 2.0.0.2. Assume 1.0.0.1 is default gateway for router, running Mikrotik RouterOS and 2.0.0.1 is default gateway for router running Cisco IOS or Cisco PIX Firewall, running Cisco PIX OS. This configuration tested and works well with Mikrotik RouterOS 3.20, Cisco IOS 12.4(21) and 12.3(26) advanced security features set with encryption and PIX OS 6.3(5).
Configuration of router running Mikrotik RouterOS
This configuration is simple and very similar to official 3.0 ipsec manual page
Mikrotik Router
Add addresses on interfaces
[admin@Mikrotik] > ip address add \
address=1.0.0.2/30 broadcast=1.0.0.3 disabled=no \
interface=public network=1.0.0.0
[admin@Mikrotik] > ip address add \
address=172.22.1.1/24 broadcast=172.22.1.255 disabled=no \
interface=inside network=172.22.1.0
Add ip routes
[admin@Mikrotik] > ip route add \
disabled=no distance=1 dst-address=0.0.0.0/0 gateway=1.0.0.1 \
scope=30 target-scope=10
Add accept and masquerading rules in SRC-NAT
[admin@Mikrotik] > ip firewall nat add \
chain=srcnat \
src-address=172.22.1.0/24 \
dst-address=172.22.2.0/24 action=accept
[admin@Mikrotik] > ip firewall nat add \
chain=srcnat out-interface=public action=masquerade
Add peer (with phase1 configuration parameters), DES and SHA1 will be used to protect IKE traffic for MikroTik router
[admin@MikroTik] > ip ipsec peer add \
address=2.0.0.2 secret="gvejimezyfopmekun" enc-algorithm=des
Set encryption proposal (phase2 proposal - settings that will be used to encrypt actual data) to use DES to encrypt data for MikroTik router
[admin@MikroTik] > ip ipsec proposal set default enc-algorithms=des
Add policy rule that matches traffic between subnets and requires encryption with ESP in tunnel mode for MikroTik router
[admin@MikroTik] > ip ipsec policy add \
src-address=172.22.2.0/24 \
dst-address=172.22.1.0/24 \
action=encrypt \
tunnel=yes sa-src=1.0.0.2 sa-dst=2.0.0.2
Add firewall rules to permit VPN traffic and private traffic
[admin@Mikrotik] >ip firewall add \
action=accept chain=input disabled=no protocol=ipsec-esp src-address=2.0.0.2
[admin@Mikrotik] >ip firewall add \
action=accept chain=customer disabled=no dst-address=172.22.1.0/24 \
in-interface=public out-interface=inside src-address=172.22.2.0/24
Cisco PIX Firewall configuration
I think this configuration is quiet clear because of detailed comments.
Cisco PIX Firewall
PIX Version 6.3(5)
nameif ethernet0 outside security0
nameif ethernet1 inside security100
!
!--- Create access list that matches traffic that should be encrypted (traffic to RouterOS device)
access-list myacl permit ip 172.22.2.0 255.255.255.0 172.22.2.0 255.255.255.0
!
!--- Create access list that matches traffic that should not be NATed (traffic to RouterOS device)
access-list nonat permit ip 172.22.2.0 255.255.255.0 172.22.1.0 255.255.255.0
!
!--- Configuring NAT
ip address outside 2.0.0.2 255.255.255.252
ip address inside 172.22.2.1 255.255.255.0
!
global (outside) 1 2.0.0.2
!
!--- Do not make NAT for traffic to RouterOS device
nat (inside) 0 access-list nonat
nat (inside) 1 172.22.2.0 255.255.255.0 0 0
!
route outside 0.0.0.0 0.0.0.0 2.0.0.1 1
!
sysopt connection permit-ipsec
!
!--- Create IPsec transform set - transformations that should be applied to
!--- traffic - ESP encryption with DES and ESP authentication with SHA1
!--- This must match "/ip ipsec proposal"
crypto ipsec transform-set myset esp-des esp-sha-hmac
crypto ipsec security-association lifetime seconds 1800
!
!--- Create crypto map that will use transform set "myset", use peer 1.0.0.2
!--- to establish SAs and encapsulate traffic and use access-list myacl to
!--- match traffic that should be encrypted
crypto map mymap 21 ipsec-isakmp
crypto map mymap 21 match address myacl
crypto map mymap 21 set peer 1.0.0.2
crypto map mymap 21 set transform-set myset
crypto map mymap interface outside
!
!--- Configure ISAKMP policy (phase1 config, must match configuration
!--- of "/ip ipsec peer" on RouterOS).
isakmp enable outside
!--- Add preshared key to be used when talking to RouterOS
isakmp key gvejimezyfopmekun address 1.0.0.2 netmask 255.255.255.255
isakmp identity address
isakmp policy 20 authentication pre-share
isakmp policy 20 encryption des
isakmp policy 20 hash md5
isakmp policy 20 group 2
: end
Corresponding Cisco Router configuration
This configuration is just for example. You can use Cisco router instead Cisco PIX Firewall.
Cisco Router
!--- Configure ISAKMP policy (phase1 config, must match configuration
!--- of "/ip ipsec peer" on RouterOS). Note that DES is default
!--- encryption algorithm on Cisco. SHA1 is default authentication
!--- algorithm
crypto isakmp policy 20
authentication pre-share
hash md5
exit
!
!--- Add preshared key to be used when talking to RouterOS
crypto isakmp key gvejimezyfopmekun address 1.0.0.2
!
! Create IPsec transform set - transformations that should be applied to
! traffic - ESP encryption with DES and ESP authentication with SHA1
! This must match "/ip ipsec proposal"
crypto ipsec transform-set myset esp-des esp-sha-hmac
mode tunnel
exit
!
!
!--- Create crypto map that will use transform set "myset", use peer 1.0.0.2
!--- to establish SAs and encapsulate traffic and use access-list 101 to
!--- match traffic that should be encrypted
crypto map mymap 21 ipsec-isakmp
set peer 1.0.0.2
set transform-set myset
set pfs group2
match address 101
exit
!
!
!--- And finally apply crypto map to outside interface
interface Ethernet0
ip address 2.0.0.2 255.255.255.252
no ip directed-broadcast
ip nat outside
crypto map mymap
!
interface Ethernet1
ip address 172.22.2.1 255.255.255.0
no ip directed-broadcast
ip nat inside
!
!
!--- Create NAT pool
ip nat pool mypool 2.0.0.2 2.0.0.2 netmask 255.255.255.252
!
!--- Do not make NAT for traffic to RouterOS device
ip nat inside source route-map nonat pool mypool overload
ip classless
ip route 0.0.0.0 0.0.0.0 2.0.0.1
!
!--- Create access list that matches traffic that should be encrypted (traffic to RouterOS device)
access-list 101 permit ip 172.22.2.0 0.0.0.255 172.22.1.0 0.0.0.255
!
!--- Create access list that matches traffic that should not be NATed (traffic to RouterOS device):
access-list 102 deny ip 172.22.2.0 0.0.0.255 172.22.1.0 0.0.0.255
access-list 102 permit ip 172.22.2.0 0.0.0.255 any
!
!--- Create route-map for traffic that should be NATed
route-map nonat permit 10
match ip address 102
!
end


Комментариев нет:
Отправить комментарий